Identity Mules — Overview
BixeLab / Biometix — Fraud & eIDV Controls
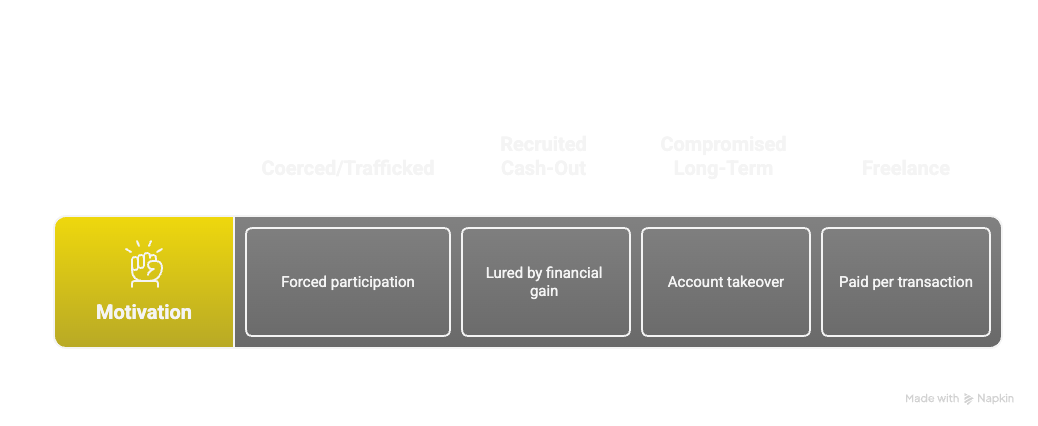
What are Identity Mules?
- Definition: People (wittingly or unwittingly) who allow their identity, accounts or payment instruments to be used to receive, move or launder funds or to obtain services for a third party.
- Impact on eIDV & banking: bypasses KYC, enables fraud/AML activity, increases chargebacks, regulatory exposure, and reputational risk.
How to pick / detect identity mules
|
Onboarding signals
- Occupation / declared profile inconsistent with transaction volumes. - Multiple applications from same device/IP but different names. - Recycled / low-quality documents; minimal address or credit history. |
Behavioural & technical signals - Rapid receive → forward pattern (short dwell time). - Transfers to high-risk corridors, crypto platforms or third-party wallets. - Device / SIM churn, emulator or remote access indicators, inconsistent geo / latency vs claimed address. |
Controls — Strengthen eIDV & Banking systems
-
Stronger identity proofing
- Document + biometric liveness + authoritative PII sources (credit bureau, govt).
-
Device & session binding
- Device fingerprinting, hardware attestation, persistent binding for high-risk flows.
-
Behavioural monitoring & network analysis
- Real-time ML scoring, link analysis for clusters & velocity anomalies.
-
Document & media forensics
- Tamper checks, deepfake/video injection detection, time/geolocation consistency checks.
-
Operational policies
- Tiered limits, EDD triggers, transaction holds, rapid suspension + STR/SAR reporting.
Practical Playbook & KPIs
Tactical
- Implement velocity caps, device-binding checks, doc quality gates, and transaction tagging.
Technical (mid-term)
- Deploy behavioral models, cluster analytics, device attestation, and stronger vendor feeds (SIM/phone intelligence, sanctions, PEP).
Governance (long-term)
- Red-team onboarding flows, cross-industry intel-sharing, periodic rule updates, and training for fraud/KYC teams.
KPIs
- % flagged accounts confirmed as mules, time-to-detection, false positive rate, reduction in illicit inflows.
Suggested Next Steps
- Apply simple onboarding rules (velocity/device checks) to new accounts.
- Instrument data capture for link/network analysis (store hashed device IDs, transaction graphs).
- Build an EDD workflow: automatic triage → human review → escalation (holds / SAR).
- Schedule regular red-team exercises to stress-test onboarding & cash-out flows.
Identity Mules
By Ted Dunstone
Identity Mules
- 119



